Intro
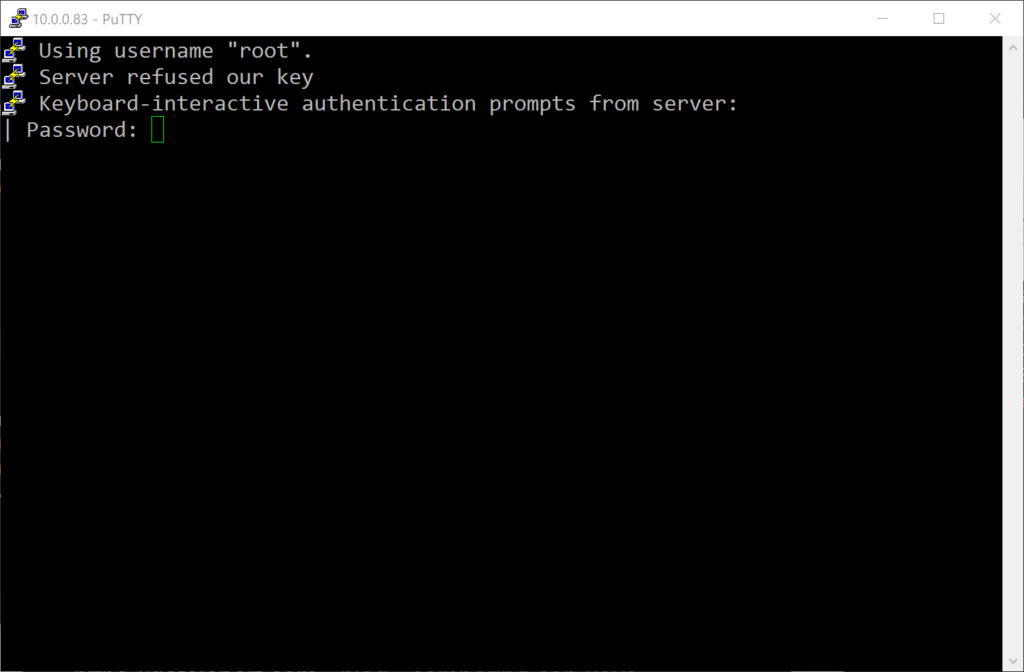
I was trying to enable SSH key-based authentication on a Photon OS VM I created on my ESXi host. After adding my public key in the authorized_keys file, it still would not let me login with my private key. All I got was: "server refused our key."
TL;DR:
运行sshd时启用debug可以提供更多有用的信息。请使用通过比较安全的算法(例如ECDSA或ED25519)生成的私钥。
Running sshd with debug flag helps reveal the cause. Make sure to use a key generated by a secure algorithm (e.g., ECDSA or ED25519).
Solution
A quick Google search brought me nowhere. The common cause (1,2,3) seems to be incorrect permissions set for the authorized_keys file, which prevents sshd from reading the public keys. I tried chmod and moving the file around, neither helped.
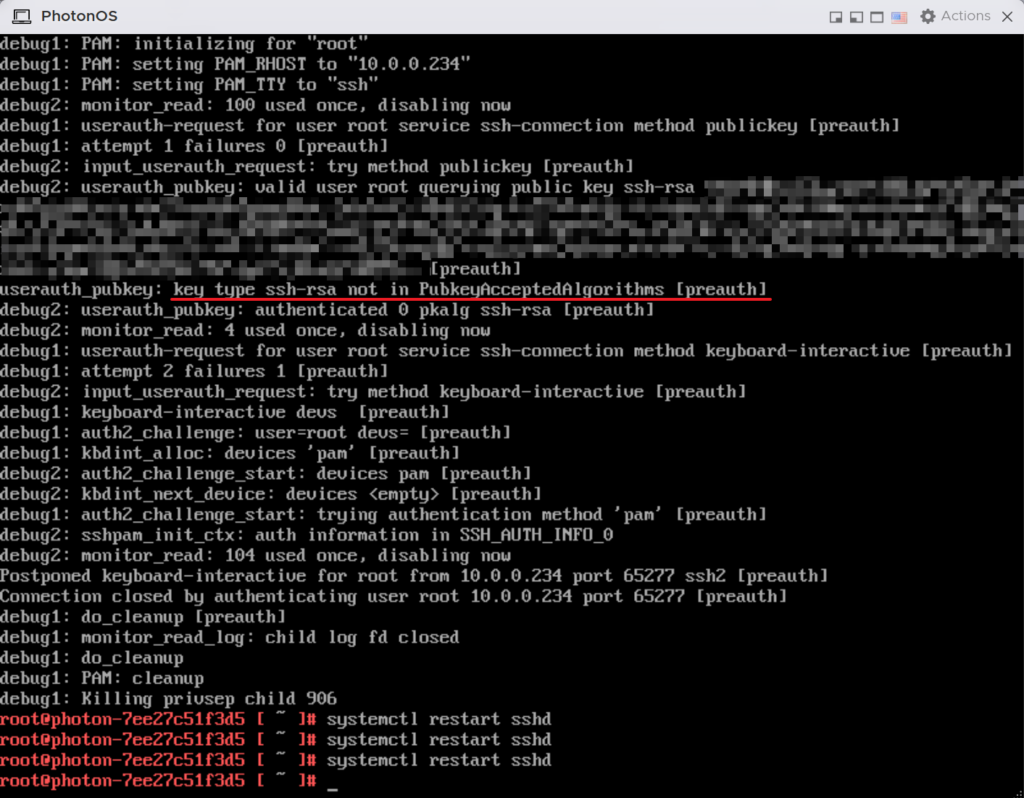
Eventually I decided to see if I can get any more useful information out of sshd. Strangely, enabling LOGLEVEL Debug3 in /etc/ssh/sshd_config did nothing. No log file was generated in /var/log.
The only option left is to kill the sshd daemon and run it interactively in debug mode to observe the output. This can be done as follows:
# find absolute path of sshd and run it with the -dd flag (Debug2)
`which sshd` -ddThen I restarted the putty session and found the root cause of the "server refused our key" message.
userauth_pubkey: key type ssh-rsa not in PubkeyAcceptedAlgorithms [preauth]It looks like the algorithm (ssh-rsa) used to generate my key is not accepted.
Obvious "Solution"
The obvious solution would be to add ssh-rsa to the accepted algorithm list. However, as pointed out by this article, the main reason why the ssh-rsa (SHA-1) algorithm is no longer accepted by default is because it was deprecated due to security vulnerabilities.
Correct Solution
The correct solution is to use a key generated with a secure algorithm such as ECDSA and ED25519. You can do this with either PUTTYGEN.EXE or ssh-keygen -t ecdsa.
References
- https://askubuntu.com/questions/306798/trying-to-do-ssh-authentication-with-key-files-server-refused-our-key
- https://askubuntu.com/questions/981285/ubuntu-server-refused-my-ssh-key-what-might-i-be-missing
- https://askubuntu.com/questions/1286622/passwordless-ssh-config-gives-server-refused-our-key
- https://support.cpanel.net/hc/en-us/articles/4402832130967-How-to-enable-debug-logging-for-SSHD-SSH-by-editing-the-etc-ssh-sshd-config
- https://www.ibm.com/support/pages/configuring-sshd-debug-mode
- https://confluence.atlassian.com/bitbucketserverkb/ssh-rsa-key-rejected-with-message-no-mutual-signature-algorithm-1026057701.html
- https://www.chiark.greenend.org.uk/~sgtatham/putty/latest.html